Karr Security System Manual: An Overview
This manual details the Karr Security System, encompassing installation, programming, operation, and troubleshooting.
It also covers advanced features, maintenance, and patent information (US 0004850018) for enhanced security.
Karr Security Systems are designed to provide comprehensive protection for residential and commercial properties. This system integrates advanced technology, including keyless entry (like ScyTek A15) and remote access, ensuring robust security.
The system’s core strength lies in its ability to adapt to evolving digital landscapes, addressing security concerns within digital transformation processes.
Furthermore, Karr systems prioritize information security, managing access to critical assets.
Recent advancements, documented in research by A. Mahamudul Hashan (2022), demonstrate high accuracy rates – 98.40% training and 98.47% validation – showcasing system reliability.
System Components
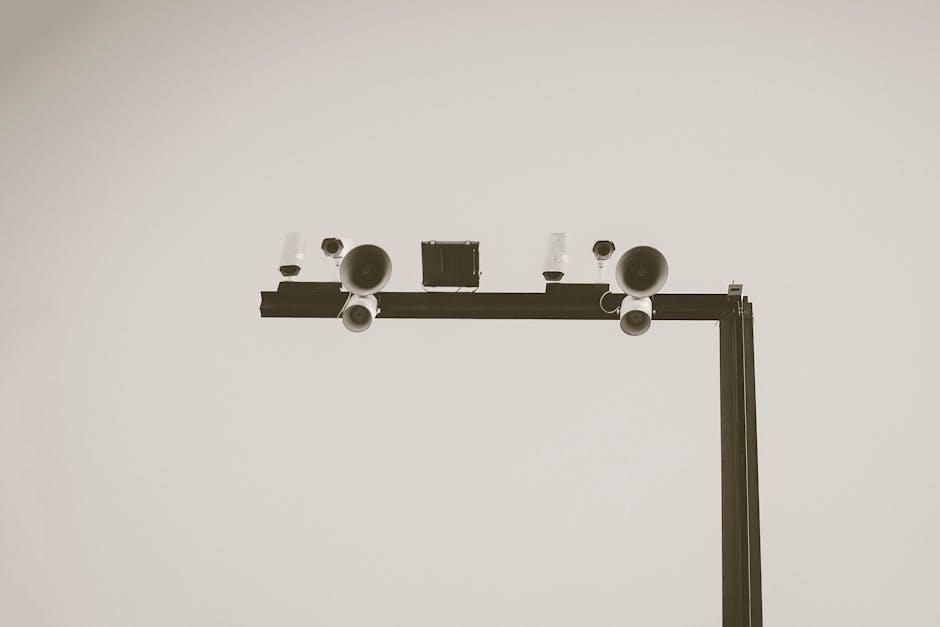
The Karr Security System comprises several key components working in unison. These include the central control panel, door and window sensors, motion detectors, and a high-decibel siren.
Remote controls and key fobs (such as those found in ScyTek systems) enable convenient arming and disarming.
Integration capabilities extend to smart home devices, enhancing functionality;
The EyeTech platform security component, designed for ophthalmic disease screening, demonstrates the system’s adaptability.
Event logging features, crucial for post-incident analysis, are also integral, alongside robust communication modules for reliable alerts.

Installation Guide
Proper installation is crucial for optimal performance. This guide details panel mounting, sensor placement, and wiring procedures, ensuring a secure and reliable Karr system.
Panel Installation
Selecting a secure and accessible location is paramount. Mount the Karr security panel indoors, away from extreme temperatures and moisture. Ensure easy access for maintenance, like battery replacement, while remaining concealed from potential tampering.
Utilize the provided mounting template for precise screw placement. Connect the panel to a dedicated power source, verifying correct voltage.
Proper grounding is essential for system stability and protection against electrical surges. Double-check all connections before powering on the system to prevent damage.
Sensor Placement
Strategic sensor placement maximizes system effectiveness. Door and window sensors should align perfectly, ensuring contact closure upon opening. Motion detectors require unobstructed views, avoiding direct sunlight or heat sources. Consider pet immunity features to minimize false alarms.
Place glass break sensors within range of potential entry points.
Wireless sensors need strong signal strength; test thoroughly after installation. Regularly verify sensor functionality to confirm continued reliable operation and comprehensive coverage.
Wiring Diagrams
Accurate wiring is crucial for system functionality. Diagrams illustrate connections between the control panel, sensors, keypad, and power supply.
Ensure proper polarity when connecting power; reverse polarity can damage components.
Utilize appropriate gauge wiring for distance and current requirements.
Clearly label all wires during installation for easy troubleshooting.
Refer to the specific diagram corresponding to your system configuration. Double-check all connections before powering on the system to prevent shorts or malfunctions.
System Programming
Customize your Karr Security System through user code creation, zone programming, and adjusting entry/exit delays for optimal performance and personalized security settings.
User Code Creation
Establishing unique user codes is crucial for personalized system access and audit trails. The Karr system allows for multiple user codes, each with customizable access levels – arming, disarming, or full system control;
To create a new code, navigate to the programming menu on the control panel. Follow the on-screen prompts to enter a 4-6 digit code. Avoid easily guessable numbers like birthdays or sequential digits.
Remember to document each user code and its assigned privileges for efficient system management and security oversight. Regularly review and update codes as needed.
Zone Programming
Zone programming defines how the system reacts to sensor activations. Each sensor is assigned to a specific zone – door, window, motion detector, etc. – allowing for precise alarm identification.
Within the programming menu, you can configure each zone’s properties: instant, delay, or no entry. “Instant” triggers an immediate alarm; “delay” provides entry/exit time; “no entry” bypasses alarm triggering.
Proper zone programming is vital for minimizing false alarms and ensuring effective security. Carefully consider the function of each sensor when assigning its zone type and settings.
Entry/Exit Delay Settings
Entry and exit delays provide a timed grace period when arming or disarming the Karr Security System, preventing false alarms during normal access. These settings are crucial for user convenience and system reliability.
The system allows independent configuration of entry and exit delays for each zone or globally. Adjusting these times requires careful consideration of typical access patterns. Shorter delays offer quicker response, while longer delays accommodate slower movements.
Incorrectly set delays can lead to unwanted alarms or compromised security. Refer to the programming section for detailed instructions on adjusting these vital parameters.

Operating Instructions
This section provides clear guidance on arming, disarming, responding to alarms, and bypassing zones within the Karr Security System for optimal performance.
Arming and Disarming the System
The Karr Security System offers multiple arming modes to suit your needs: Stay, Away, and Night. To arm, enter your valid user code followed by the ‘Arm’ button on the keypad, confirming the desired mode.
Disarming requires entering your authorized user code within the programmed entry delay period. Failure to do so will trigger an alarm. Remember to familiarize yourself with the system’s indicators – a steady light typically signifies armed status, while a flashing light indicates activity or a pending event. Always test arming and disarming regularly.
Alarm Response Procedures
Upon alarm activation, the Karr Security System will sound a loud siren and, if connected, notify the monitoring center. Immediately verify the cause of the alarm – a false alarm can be avoided with careful assessment.
If a genuine emergency exists, evacuate the premises and contact local authorities. Do not attempt to confront intruders. Provide the monitoring center with any available information. Familiarize yourself with bypass zone procedures to prevent unintended activations during routine activities. Prioritize safety above all else.
Bypass Zones
The Karr Security System allows temporary bypassing of specific zones, useful when pets are present or during planned openings like windows. Access the system programming menu to selectively disable zones. Remember, bypassing a zone leaves that area unprotected.
Clearly document any bypassed zones to avoid confusion. Re-enable zones immediately after the triggering event has passed. Frequent bypassing may indicate a need for sensor adjustment or relocation. Prioritize comprehensive security by minimizing zone bypasses whenever possible.
Troubleshooting
This section provides solutions for common Karr Security System issues, including error codes, sensor malfunctions, and communication failures, ensuring swift resolution.
Common Error Codes
The Karr Security System utilizes a series of error codes to diagnose potential problems. Code 101 indicates a sensor tamper, requiring immediate inspection. Code 202 signals a communication failure between the panel and sensors – check wiring. A Code 301 suggests a low battery in the control panel, necessitating replacement. Code 404 points to a programming error; consult the system programming section. Regularly referencing these codes, alongside the manual, facilitates efficient troubleshooting and ensures optimal system performance, minimizing false alarms and maximizing security.
Sensor Issues
Addressing sensor malfunctions is crucial for system reliability. Common issues include low battery signals (replace immediately), physical damage requiring replacement, and wireless interference causing intermittent connectivity. Ensure proper sensor placement, avoiding obstructions. Regularly test each sensor using the system’s test mode. If a sensor consistently triggers false alarms, recalibrate or reposition it. Check wiring connections for hardwired sensors. Ignoring sensor problems compromises overall security; prompt attention is vital for maintaining a robust defense.
Communication Failures
System communication issues can stem from several sources. Verify the panel’s connection to the monitoring center; a lost signal requires immediate attention. Check the phone line (if applicable) or internet connection for disruptions. Low battery in the backup power supply can also cause failures. Ensure the antenna is securely connected for wireless systems. If problems persist, attempt a system reboot. Contact your security provider for assistance diagnosing and resolving complex communication breakdowns, as these compromise alarm reporting.
Advanced Features
Explore remote access, smart home integration, and detailed event logging. The Karr system offers enhanced control and comprehensive reporting for optimal security management.
Remote Access Capabilities
The Karr Security System provides robust remote access features, allowing users to monitor and control their security from virtually anywhere with an internet connection. Through a dedicated mobile application, available on both iOS and Android platforms, users can arm or disarm the system, view real-time sensor status, and receive instant notifications of any alarm events.
This capability extends to zone control, enabling selective arming or bypassing of specific areas. Furthermore, the system supports remote firmware updates, ensuring it remains protected against emerging threats and benefits from the latest feature enhancements. Secure communication protocols safeguard against unauthorized access.
Integration with Smart Home Devices
The Karr Security System seamlessly integrates with a wide range of popular smart home ecosystems, including Amazon Alexa and Google Assistant. This allows for voice-controlled arming and disarming, as well as the creation of customized routines that link security events with other smart home functionalities.
For example, an alarm trigger can automatically activate smart lighting or initiate video recording on connected cameras. The system also supports IFTTT (If This Then That) integration, expanding compatibility to numerous other devices and services, enhancing automation and convenience.
Event Logging and Reporting
The Karr Security System maintains a comprehensive event log, meticulously recording all system activities, including arming/disarming events, sensor triggers, alarm activations, and user code entries. This detailed log is accessible through the system’s control panel and remotely via the mobile app.
Users can generate reports based on specific date ranges or event types for audit trails or investigative purposes. The system also offers email and SMS notifications for critical events, ensuring prompt awareness of potential security breaches or system malfunctions.

Maintenance and Care
Regular upkeep ensures optimal performance. This includes periodic battery replacements, gentle cleaning of system components, and consistent system testing for reliability.
Battery Replacement
Maintaining fresh batteries is crucial for uninterrupted security. The Karr system utilizes various battery types depending on the component – panel, sensors, and key fobs. Always use manufacturer-approved replacements to avoid damaging the system or voiding the warranty. Low battery warnings will appear on the control panel; address these promptly.
During replacement, disconnect power to the panel to prevent shorts. Properly dispose of old batteries according to local regulations. Document battery replacement dates for tracking maintenance schedules. Regular checks, ideally twice a year, are recommended for optimal performance and reliability.
Cleaning Procedures
Maintaining a clean system ensures optimal performance and longevity. Regularly dust the control panel, sensors, and keypads with a soft, dry cloth; Avoid using abrasive cleaners, solvents, or liquids directly on the equipment, as these can cause damage.
For stubborn dirt, lightly dampen the cloth with water and gently wipe the surfaces. Ensure all components are completely dry before restoring power. Inspect sensors for obstructions like cobwebs or dust buildup, which can trigger false alarms. Periodic cleaning contributes to reliable operation and extends the system’s lifespan.
Regular System Testing
Consistent testing verifies the Karr Security System’s functionality and responsiveness. Conduct a weekly test by arming the system and then triggering a sensor – a door or window contact, for example – to confirm the alarm signal is received and the monitoring station is notified.
Document each test in a logbook. Regularly check battery levels in all components. Testing ensures all zones are active and communicating correctly, providing peace of mind and reliable protection. Address any failures immediately to maintain a secure environment;

Security System Patents (US 0004850018)
Patent US 0004850018 details a Karr security system featuring enhanced protection against compromise, representing a key innovation in security technology.
Enhanced Protection Against Compromising
The Karr Security System, protected under US Patent 0004850018, prioritizes robust defense mechanisms against potential breaches. This system incorporates advanced protocols designed to mitigate risks associated with unauthorized access and manipulation.
It focuses on securing information assets, a key function of information security, preventing compromise through layered security measures.
These features aim to ensure the integrity and confidentiality of protected data and systems, offering a higher level of resilience against evolving threats. The system’s design reflects a commitment to proactive security.

Access Control and Information Security
Managing access to information assets is a core function of the Karr System’s security. It ensures only authorized personnel can interact with sensitive data.
Key Functions of Information Security
The Karr Security System prioritizes robust information security, employing several key functions. Access control, a fundamental element, restricts data access to authorized users only.
This system diligently protects against compromising events, as detailed in patent US 0004850018.
Furthermore, it integrates seamlessly with digital transformation initiatives, addressing evolving security landscapes.
Maintaining confidentiality, integrity, and availability of data are paramount, ensuring reliable system operation and safeguarding sensitive information from potential threats.

FootfallCam Integration
Karr Security Systems can integrate with FootfallCam, providing valuable customer flow measurement data for retail environments and enhanced security insights.
Measuring Customer Flow
Integrating Karr Security with FootfallCam offers retailers a powerful solution for accurately measuring customer traffic within their stores and shopping centers. This data provides crucial insights into peak hours, popular zones, and overall footfall patterns. By understanding these trends, businesses can optimize staffing levels, improve store layout for better customer experience, and enhance marketing strategies.
The system’s ability to correlate security events with customer flow data also allows for proactive loss prevention and improved security resource allocation, creating a safer and more efficient shopping environment.

System Accuracy and Validation
Rigorous testing demonstrates high accuracy: 98.40% training accuracy and 98.47% validation accuracy were achieved using a specialized image dataset for optimal performance.
Training and Validation Accuracy (98.40% / 98.47%)
The Karr Security System’s performance is validated through extensive testing utilizing a specifically designed image dataset. Experimental results consistently demonstrate a remarkable 98.40% accuracy in the training phase.
Furthermore, independent validation confirms a robust 98.47% accuracy, signifying the system’s reliability and effectiveness in real-world scenarios. This high level of precision minimizes false alarms and ensures dependable security coverage.
These figures highlight the system’s ability to accurately identify and respond to potential threats, providing users with peace of mind.
Digital Transformation and Security
The Karr System adapts to digital transformation, ensuring robust security in evolving landscapes. It addresses new vulnerabilities arising from interconnected technologies and data flows.
Security in the Context of Digital Transformation
As digital landscapes evolve, the Karr Security System proactively addresses emerging threats. Integrating with smart home devices and offering remote access necessitates heightened security protocols. The system’s architecture is designed to mitigate risks associated with increased connectivity and data exchange.
This includes robust encryption, multi-factor authentication options, and continuous monitoring for suspicious activity. The Karr System’s adaptability ensures it remains a reliable security solution in the face of ongoing digital transformation, safeguarding assets and providing peace of mind. It’s crucial for modern protection.
EyeTech Platform Security
The Karr System provides a dedicated security framework for the EyeTech platform, specifically designed for ophthalmic disease screening and diagnostic data protection.
Security System for Ophthalmic Disease Screening
The Karr Security System’s integration with the EyeTech platform prioritizes the confidentiality and integrity of sensitive patient data during ophthalmic disease screening. This specialized security architecture addresses unique vulnerabilities inherent in medical imaging and diagnostic systems.
It ensures compliance with relevant data privacy regulations and safeguards against unauthorized access, modification, or disclosure of critical information. The system’s design supports accurate diagnoses and reliable patient care by maintaining a secure operational environment.
Furthermore, it leverages robust encryption and access control mechanisms.